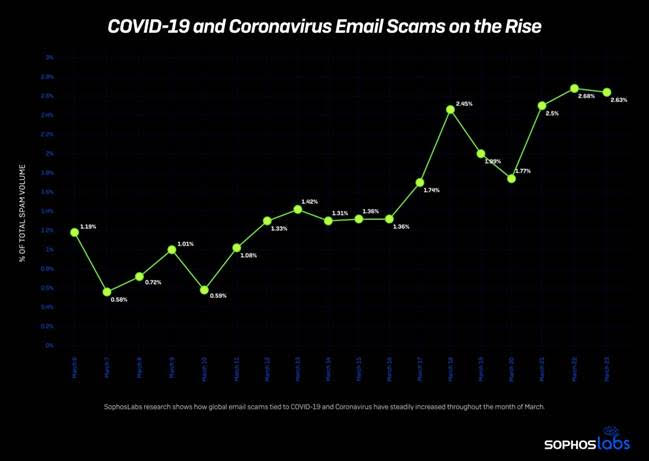
SophosLabs is tracking how the use of “COVID-19” and “coronavirus” in domain names, spam, phishing attacks, and malware has skyrocketed, nearly tripling in the past week.
Attackers are also increasingly impersonating the World Health Organization (WHO), Centers for Disease Control and Prevention (CDC), North America, and the United Nations (UN), as evidenced in scams tracked by SophosLabs. Attached are a few new examples.
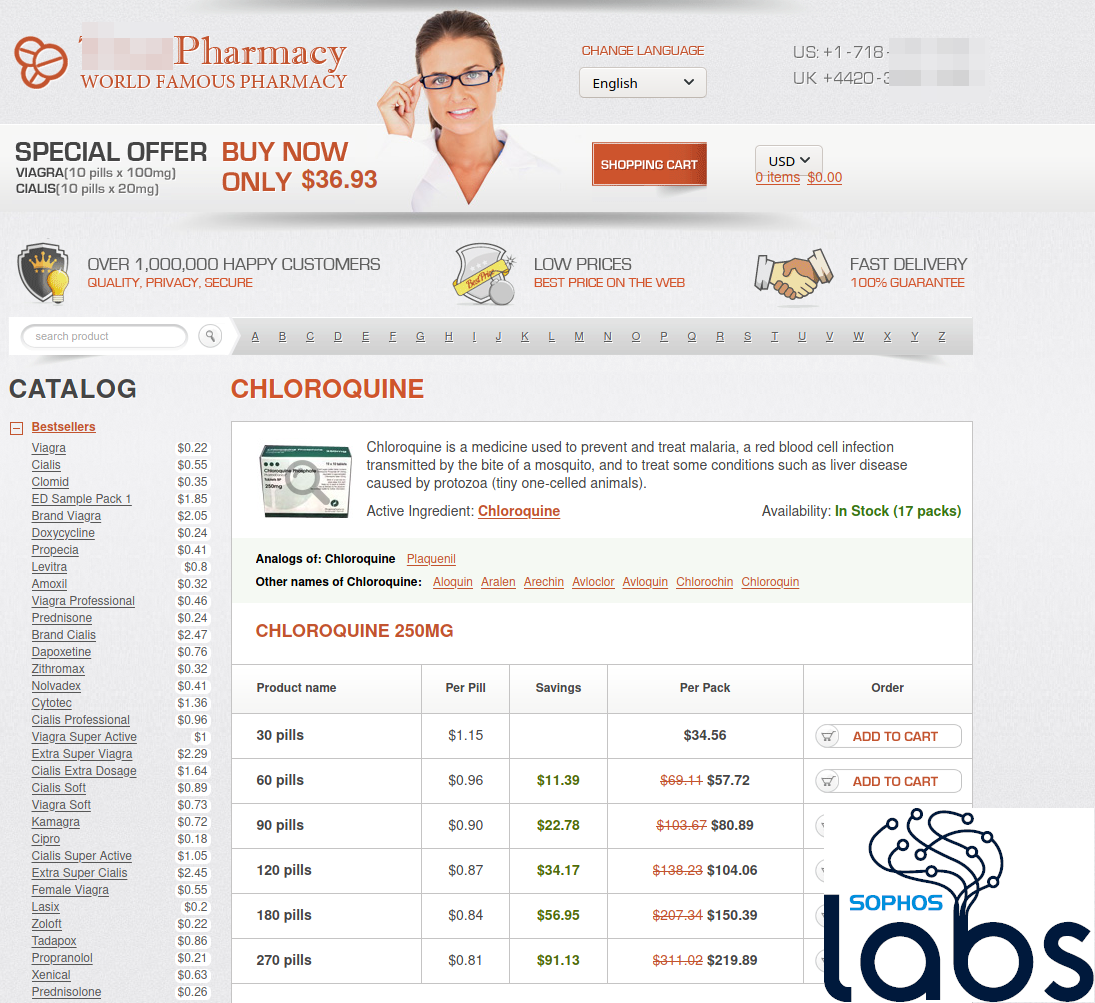
“Cybercriminals are wasting no time in shifting their dirty, tried and true attack campaigns toward advantageous lures that prey on mounting virus fears. It’s easy to see, for example, that the attackers behind a new Chloroquine scam are the same as those behind a recent herbal Viagra scam,” according to Sophos principal research scientist Chester Wisniewski.
“With global spam volumes estimated to be in the hundreds of billions, for 2-3% of those to be COVID-19 themed is significant. Similar to A/B testing of advertisements and web pages, criminals often dip a toe in the water when there is a new or sensational topic in the news. If the new topic proves a more effective lure than the previous scam bait they begin switching to new lures.
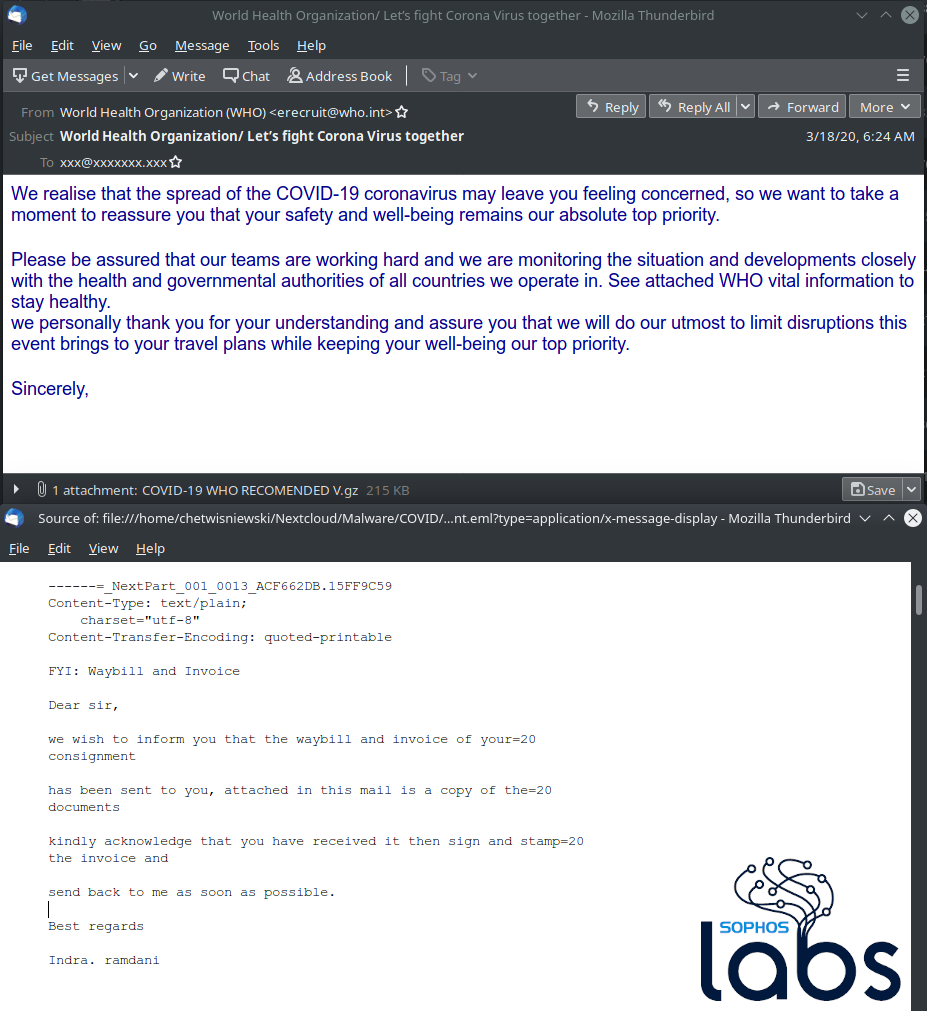
“In fact in one of the spam campaigns we tracked this week, there was evidence of exactly that. These particular criminals had been using fake shipping and delivery emails to convince unsuspecting victims into opening attachments and infecting their computers with the Kryptik Trojan. Now the main body of the email pretends to come from [email protected] with “health advice” in the attachment, but when we carefully inspect the plain text body, we see it matches a previous spam campaign from this same criminal using a lure pretending to be about invoices and deliveries.
“The increases we are seeing are likely due to two important factors. First, as time passes more and more criminal groups are joining the party on using all this interest in COVID-19 to steal money from people. Secondly, it takes time. Any given criminal group has to handcraft the spams to convince the recipient to take an action. In the research community we call this the call to action. The call to action might be to open the attachment, visit the website or, in the case of the WHO Bitcoin scam, to donate cryptocurrencies to criminal controlled Bitcoin wallets. Crafting these messages takes time, especially for those who are not native English speakers.
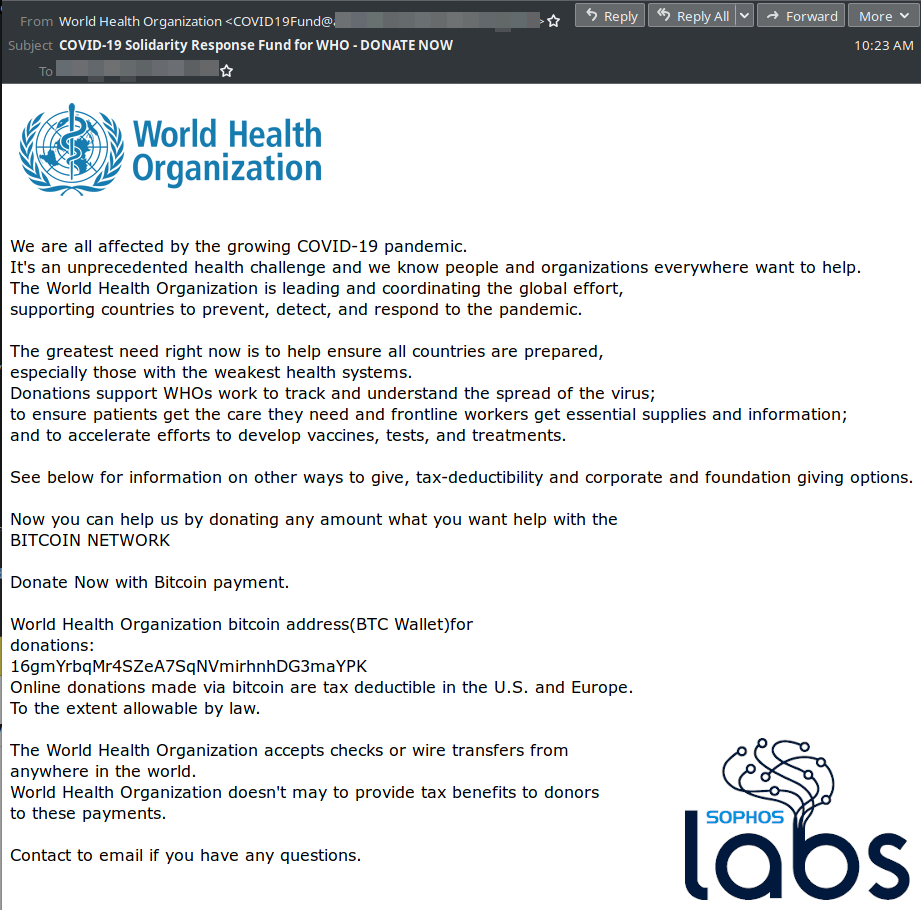
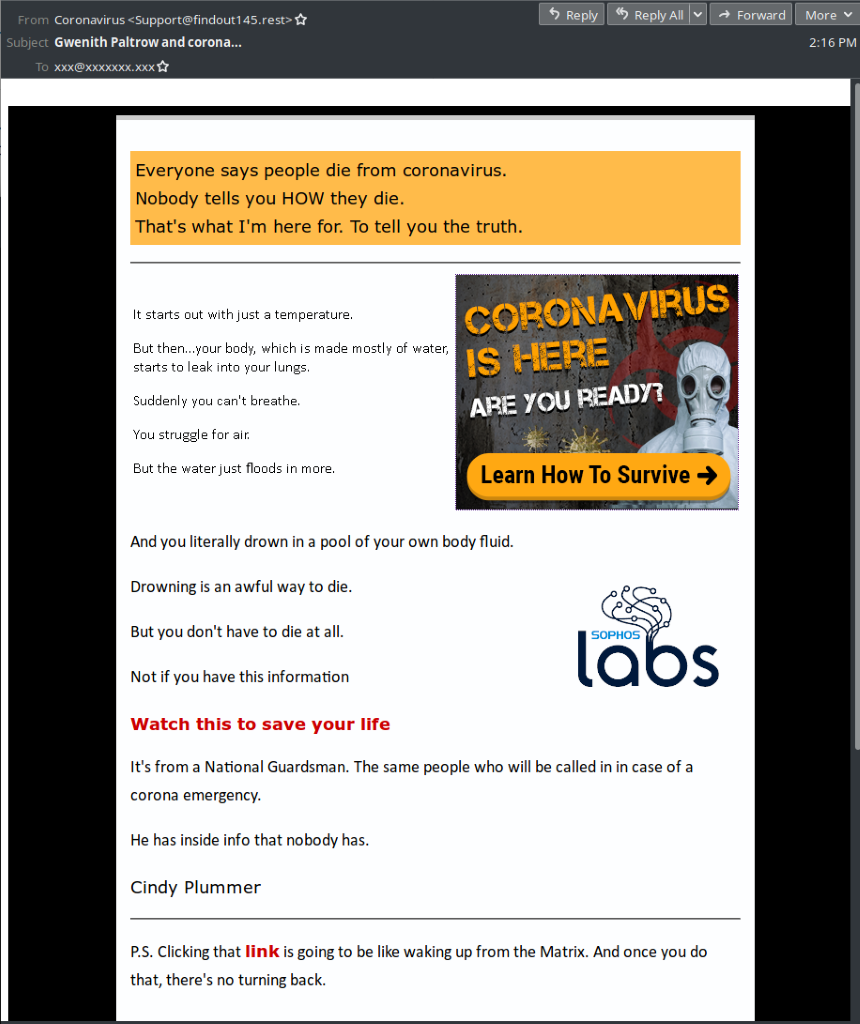
“Even the most innocuous mention of something by a politician or a celebrity can lend a scam credibility or present a new business opportunity. Two recent examples come to mind. One spam campaign offering to tell you about the government cover up and attempting to sell you a COVID-19 survival guide used celebrity Gwyneth Paltrow as a lure in its subject line. A tipoff the email is a fake is the incorrect spelling of her first name as Gwenith, but this could easily be missed or glossed over. A few days ago President Donald Trump mentioned the possible efficacy of a drug called Chloroquine against Coronavirus immediately leading to WordPress blog comment spammers switching from pitching herbal Viagra to instead attempting to sell you Chloroquine, which can be quite dangerous when not taken under the supervision of a doctor. And within only two days of the WHO creating a charity called the Solidarity Response Fund, criminals were soliciting Bitcoin donations pretending to be the charity, even implying your donation is fully tax deductible in the US or Europe.”
SophosLabs has uncovered a variety of different malicious email campaigns connected to COVID-19, including:
- Phishing scams impersonating the WHO, CDC, and other healthcare organizations to deliver malware via malicious documents disguised as official information on how to stay safe during the pandemic
- Cybercriminals impersonating charities and relief organizations like the WHO’s COVID-19 Solidarity Response Fund to trick victims into sending them Bitcoin